IFTTT is a mobile app that will automatically do something in one app if something else happens in another app. For example, when this post gets published, IFTTT will automatically create a tweet in twitter with the post title and a link for me. All without me ever actually opening Twitter.
IFTTT isn't limited to Twitter and Blogger. In fact, there are dozens of services that IFTTT can cause to work together. I tend to think of IFTTT as a scaled down, but free and easier to learn version of Tasker. I use them both, each for different tasks.
IFTTT is useful in general, but I think there are some recipes that can be of particular use to attorneys. As I come across them, I'll write about them here.
Today's tip is how to use IFTTT to keep track of your cell phone calls by creating and keeping an automatic call log in Google Drive. This may be of more use to solo and small firm practitioners particularly, but anyone that uses a cell phone for client communications can benefit.
In IFTTT, you will need to make sure that you enable the Google Drive and Android Phone channels. Next, create a new recipe and click on the "if" statement.
Next, choose "Android Phone Call" from the list along the top. Within that, click on the plus sign next to "Any phone call placed".
Then, click on the plus for the "Then" statement.
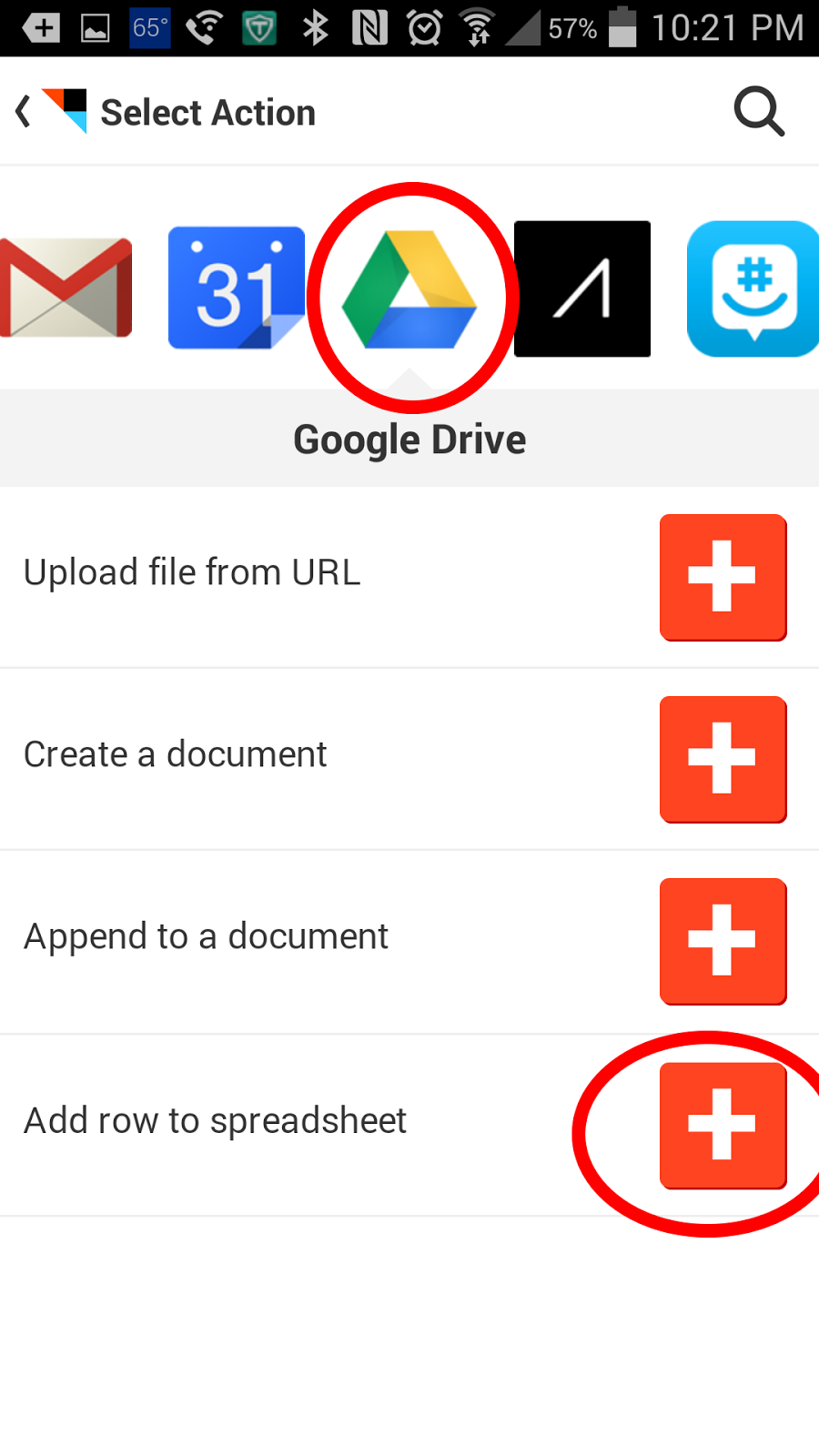
Then, scroll and find Google Drive. Click on it, and then click on "Add row to speadsheet".
What this will do is create a new spreadsheet named "Phone call" in your Google Drive account in a folder called IFTTT. It will have four columns that state when the phone call was made, what number was called, who was called, and how long it lasted. You can tweak some of this in the edit recipe menu.
How is this useful for an attorney? If you make several phone calls on the road, you can quickly enter your time into your billing or case management software by referencing a single spreadsheet. The only thing you would have to do is remember what the substance of the call was. This is much easier than going through your phone's call log an into each entry to see when the call occurred and how long it lasted for billing purposes.